3PL Data Security: How to Protect Your Supply Chain Information
Your 3PL partner has access to customer addresses, payment information, inventory data, and shipping records – but so can cybercriminals.
Third-party logistics providers face a growing wave of cyberattacks, with supply chain breaches increasing by 431% between 2021 and 2023.
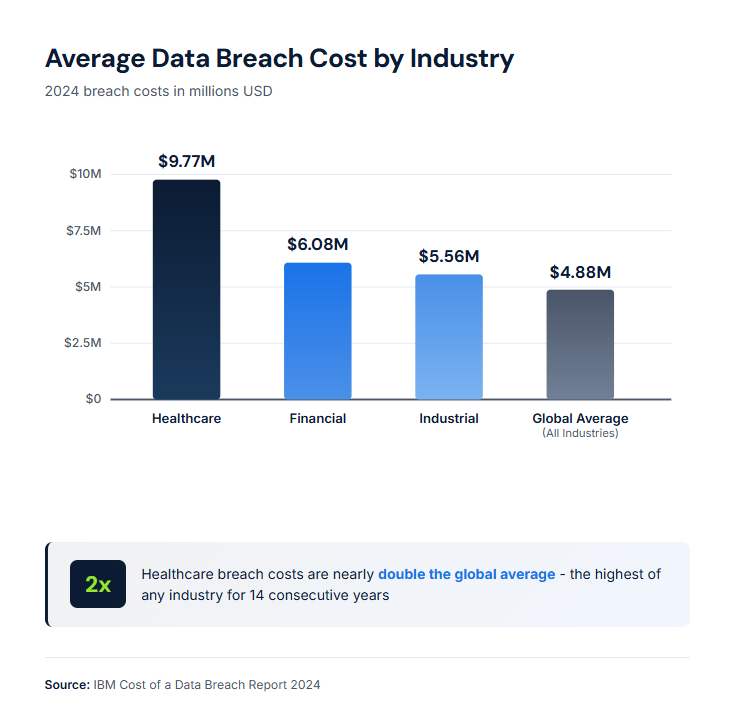
A single data breach now costs organizations an average of $4.88 million. For logistics operations handling sensitive customer information, the damage extends beyond finances to shattered client trust and operational paralysis.
In this guide, we’ll cover the key 3PL data security operations and the prevention practices that can keep your and your clients' data protected!
The Importance of Security in 3PL
Data security in third-party logistics directly impacts every business that depends on your warehousing and fulfillment services. When a 3PL experiences a breach, the ripple effects spread to every brand whose customer data and inventory records pass through your systems.
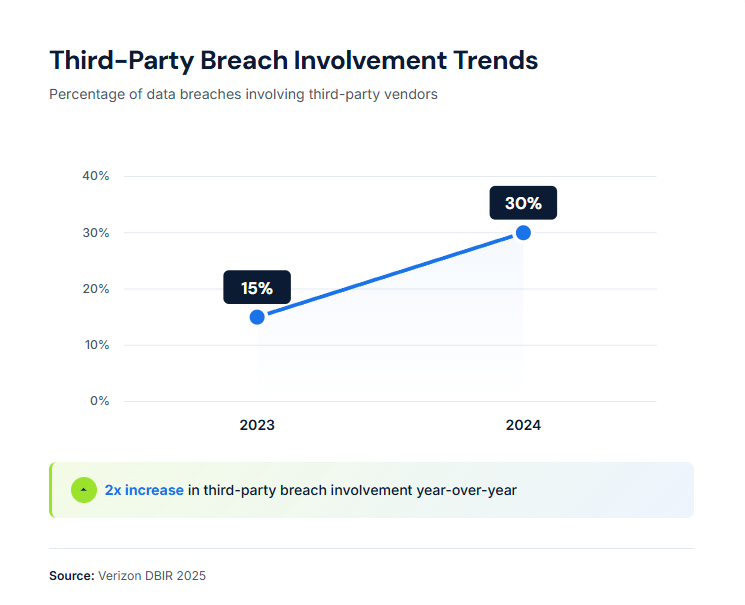
According to the 2025 Verizon Data Breach Investigations Report, 30% of all breaches now involve third parties; double the rate from the previous year. This makes 3PLs both high-value targets and potential entry points for attacks on their clients' systems.
The shipping industry experienced at least 64 cyberattacks in 2023 alone, compared to just three in 2013 and none in 2003, according to research cited by Maersk. This acceleration shows no signs of slowing, with transportation and logistics companies facing approximately 27 significant incidents between July 2023 and July 2024.
Beyond direct costs, a breach can damage your reputation as a trusted logistics partner. Brands increasingly require security certifications before entering fulfillment agreements, making data protection a competitive necessity.
8 Best Risk Prevention Practices
#1. Implement Role-Based Access Controls
For starters, you can restrict system access by job function. Warehouse staff need different permissions than billing administrators or client service representatives.
A warehouse management system (WMS) should assign individual, auditable user accounts to employees. This creates accountability and provides a clear audit trail linking specific transactions to specific individuals. When someone accesses customer shipping data or modifies inventory records, you know exactly who did it and when.
Key implementation steps include:
- Define permission levels for each role (receiving, picking, shipping, admin, client access)
- Require unique credentials for every user (no shared logins)
- Review and revoke access immediately when employees change roles or leave
- Implement the principle of least privilege (users get the minimum access needed for their job)
#2. Require Multi-Factor Authentication
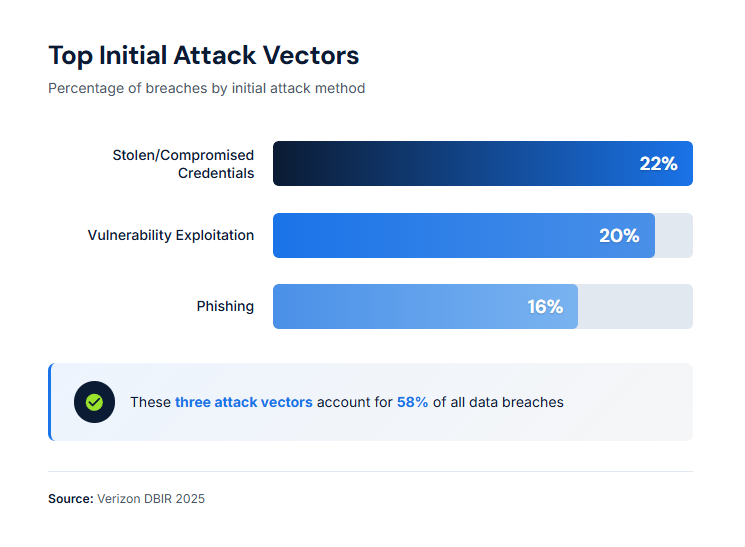
Stolen credentials remain a significant attack vector. According to the mentioned 2025 Verizon DBIR, credentials accounted for 22% of breaches, while IBM's 2024 Cost of a Data Breach Report found that breaches involving stolen credentials took an average of 292 days to identify and contain, the longest of any attack vector.
Multi-factor authentication (MFA) adds a second verification factor beyond a password. Even if attackers steal login credentials, they cannot access systems without the additional authentication factor.
Deploy MFA for:
- WMS and inventory management platforms
- Client portals and EDI connections
- VPN and remote access tools
- Email and communication systems
- Financial and billing systems
The 2025 Verizon DBIR notes that breaches involving cloud platforms often stemmed from compromised credentials and a lack of MFA, both of which are preventable security gaps.
#3. Encrypt Data at Rest and in Transit
Encryption renders stolen data unreadable without the decryption key. This protection must cover data both when it is stored in your systems (at rest) and when it is moving between systems (in transit).
For 3PL operations, encrypt:
- Customer personal information (names, addresses, phone numbers)
- Payment and billing data
- Inventory records and product information
- EDI transmissions and API connections with clients
- Shipping labels and tracking information
- Internal communications containing sensitive data
Use TLS 1.3 for data in transit and AES-256 encryption for stored data. Cloud-based WMS platforms should provide encryption as a standard feature; verify this before selecting a provider.
#4. Conduct Regular Security Audits and Penetration Testing
You cannot protect what you do not measure. Regular assessments identify vulnerabilities before attackers exploit them.
Schedule quarterly vulnerability scans and annual penetration tests conducted by independent security professionals. These tests simulate real attacks against your systems to find weaknesses.
Audit checklist for 3PL operations should include:
- Network segmentation between warehouse systems and corporate networks
- Firewall configurations and access rules
- Software patch status across all systems
- User access reviews and dormant account identification
- Physical security controls at warehouse facilities
- Vendor and client connection security
- Backup and recovery procedures
Document findings and track remediation. Many clients request audit reports as part of their vendor due diligence.
#5. Establish Incident Response Plans
Organizations with incident response teams and tested plans saved an average of $2.03 million per breach, compared with those without such teams and plans. Having a plan matters; testing that plan matters more.
Your incident response plan should define:
- Detection procedures and escalation criteria
- Roles and responsibilities during an incident
- Communication protocols (internal, clients, law enforcement, media)
- Containment and eradication steps
- Evidence preservation requirements
- Recovery procedures and business continuity measures
- Post-incident review process
Test the plan through tabletop exercises at least twice per year. Walk through realistic scenarios: a ransomware attack on your WMS, a compromised client EDI connection, or a breach of customer shipping data.
#6. Maintain Comprehensive Backup Systems
Ransomware appeared in 44% of all breaches in the 2025 Verizon DBIR, up from 32% the previous year. The median ransom payment hit $115,000, but organizations with solid backups can often avoid paying entirely.
Backup requirements for 3PL operations are:
- Daily incremental backups of all critical systems
- Weekly full backups are stored offsite or in isolated cloud storage
- Regular restoration tests to verify backup integrity
- Separation between backup systems and production networks
- Documented recovery time objectives (RTO) for each system
Keep backups isolated from your primary network. Attackers increasingly target backup systems specifically to remove the recovery option before deploying ransomware.
#7. Obtain Security Certifications
Third-party certifications demonstrate your security posture to clients and provide frameworks for continuous improvement.
Two certifications matter most for 3PL providers:
- SOC 2 Type 2. Developed by the American Institute of CPAs, this audit evaluates the design and operating effectiveness of your security controls over a 6-12 month period. SOC 2 focuses on five Trust Service Criteria: security, availability, processing integrity, confidentiality, and privacy. This certification is the standard request from U.S.-based clients.
- ISO 27001. This international standard requires the establishment and maintenance of an Information Security Management System (ISMS). International clients prefer ISO 27001, and it integrates well with other operational certifications many 3PLs already hold, such as ISO 9001 for quality management. According to the SecureFrame survey, there is approximately 80% overlap between SOC 2 and ISO 27001 controls, so pursuing both becomes more efficient after completing one.
Many enterprise clients now require one or both certifications before signing fulfillment agreements. Certification also forces the documentation and process improvements that strengthen actual security.
#8. Train Employees Continuously
The 2025 Verizon DBIR found that 60% of breaches involve the human element. Despite this, the report also found that phishing click rates remain largely unaffected by one-time training programs.
Practical security training for warehouse and logistics staff should include:
- Recognizing phishing emails and social engineering attempts
- Proper handling of customer data (both digital and physical documents)
- Password hygiene and credential management
- Reporting suspicious activity and near-misses
- Physical security awareness (tailgating, unauthorized visitors, unlocked workstations)
Make training ongoing rather than annual. Short monthly modules maintain awareness better than yearly compliance sessions. Track completion and comprehension, and include security awareness in performance evaluations.
5 Key Risk Areas in 3PL Operations
Understanding where vulnerabilities concentrate helps prioritize security investments. These five areas present significant supply chain challenges for third-party logistics providers:
- Client integration points. EDI connections, API integrations, and client portal access create entry points between your systems and client networks. A breach in either direction damages both parties. Require secure authentication for all integrations and monitor connection activity for anomalies.
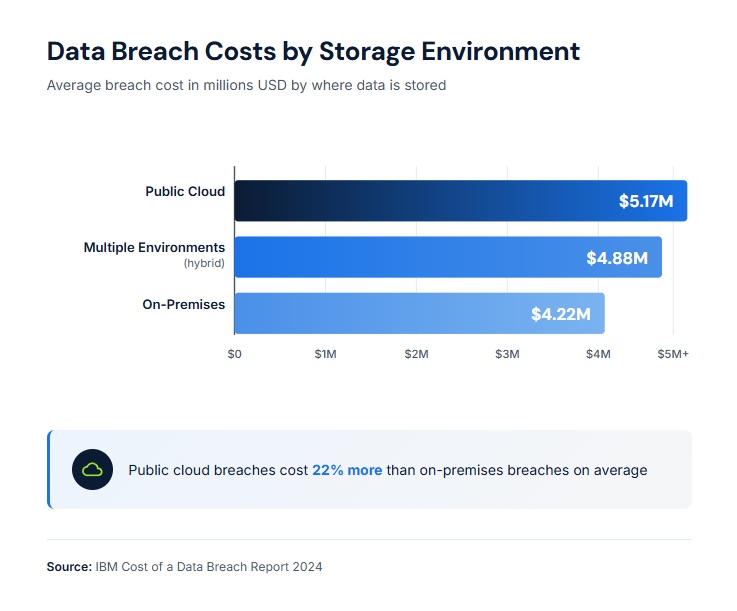
- Cloud and software platforms. Cloud-based WMS and inventory systems offer flexibility but introduce third-party risk. Breaches involving public cloud environments cost an average of $5.17 million in 2024, 13% higher than the previous year. Evaluate provider security practices, require encryption, and understand the shared responsibility model.
- Remote access and VPN. The 2025 Verizon DBIR documented an 8× increase in attacks targeting VPNs and network edge devices. Only 54% of vulnerabilities in these systems were fully patched, with a median remediation time of 32 days. Prioritize patching for remote access infrastructure and consider zero-trust alternatives.
- Third-party vendors. Your security extends only as far as your weakest vendor. Carriers, temp staffing agencies, equipment maintenance providers, and software vendors all represent potential breach vectors. Assess vendor security practices and include security requirements in contracts.
- Physical-digital intersection. Warehouse environments combine physical operations with digital systems. Unsecured workstations, printed shipping labels with customer data, and RF scanners all present risks. Apply security controls to both the physical and digital aspects of operations.
Frequently Asked Questions
#1. How long does it take to recover from a ransomware attack?
Recovery time varies based on preparation and attack severity. Organizations took an average of 21-24 days to recover from ransomware attacks, according to industry research. However, only 12% of breached organizations achieved complete recovery, with most taking over 100 days. Having tested backups and incident response plans substantially reduces recovery time.
#2. What data types are most targeted in 3PL breaches?
Personal customer information appears in 46% of all data breaches, making it the most commonly targeted data type. For 3PLs, this includes shipping addresses, contact information, and purchase details. Attackers also target credentials, intellectual property such as client contracts and pricing, and system data that enables further network access.
#3. Does cyber insurance cover 3PL data breaches?
Cyber insurance can cover breach-related costs, but policies vary significantly. Premiums increased by 50% in 2022, and insurers are increasingly requiring security controls, such as MFA and backup verification, before issuing policies. Review policy exclusions carefully, as some may not cover breaches originating from third-party vendors or exclude certain attack types.
What is the biggest security mistake 3PLs make?
Underestimating third-party and vendor risk represents the most common security gap. The 2025 Verizon DBIR found that 30% of breaches involved third parties, double the rate of the previous year. Many 3PLs focus on their own systems while overlooking risks from carriers, software vendors, temp agencies, and client connections. Comprehensive security requires extending controls across the entire partner ecosystem.
Key Takeaways
- Third-party involvement in breaches doubled to 30% in 2024, making 3PLs both targets and potential attack vectors for client networks.
- The average data breach costs $4.88 million globally; industrial-sector breaches cost $5.56 million, 14% above the average.
- Stolen credentials account for 22% of breaches and take an average of 292 days to detect; deploy MFA across all systems.
- Ransomware appeared in 44% of breaches; maintain isolated backups and test restoration procedures.
- SOC 2 and ISO 27001 certifications demonstrate a commitment to security and meet growing client requirements.
- 60% of breaches involve human factors; implement continuous security training rather than annual sessions.
- Secure client integration points, cloud platforms, VPN access, vendor relationships, and physical-digital intersections.
20 Years of Kitting Excellence
Ready to Streamline Your Supply Chain?
Join industry leaders achieving 99%+ SLA performance with flexible kitting, fulfillment, and 3PL solutions.
Get in Touch